Crypto payment security best practices help merchants protect customer payments, prevent operational mistakes, and keep checkout reliable. Crypto payments are secure by design, but the surrounding workflow—wallet access, webhooks, and order status—still requires careful handling. The goal is to create a secure system that does not slow down the customer experience.
This guide covers the practical security steps every merchant should implement when accepting crypto payments.
Crypto payment security best practices begin with access control
The fastest way to reduce risk is to limit access to payment settings. Only trusted staff should be able to view or change wallet settings, webhook secrets, or settlement preferences. Use role‑based permissions and document who has access.
For larger teams, add a two‑person approval process for high‑value changes. This prevents accidental misconfiguration and protects against internal mistakes.
Secure webhooks and order updates
Webhooks are critical for payment confirmation. If they are not secure, attackers can spoof payment events and mark orders as paid. Use signed webhook payloads and verify signatures before updating order status. Also ensure your webhook endpoint is idempotent so duplicate events do not create duplicate actions.
Logging webhook events makes it easier to audit payment issues later.
Keep pricing stable and conversion clear
Security is not only technical; it is also about clarity. Customers who are confused by the payment process are more likely to make mistakes, and mistakes create support issues. Keep pricing in fiat and calculate crypto at checkout. Show the exact amount, network, and payment window clearly.
Clear UI reduces error rates and protects your support team from avoidable workload.
Protect high‑value orders
High‑value orders require extra safeguards. Use additional confirmations or manual review for orders above a defined threshold. This is a standard practice in ecommerce and helps prevent the small number of risky orders from creating large losses.
For digital goods, delay delivery until confirmation is received. This simple rule prevents the most common abuse cases.
Wallet management and treasury security
If you hold crypto or stablecoins, treat wallets like cash accounts. Use multi‑signature wallets or approval workflows for transfers, and keep keys in secure storage. Limit the amount held in hot wallets and move larger balances to more secure storage on a schedule.
These practices reduce exposure and protect treasury operations from a single point of failure.
Incident response planning
Every payment system needs an incident response plan. Define what happens if a webhook fails, a payment is delayed, or a suspected breach occurs. Assign clear responsibilities and document a recovery checklist. This reduces panic and keeps the business running smoothly even when issues arise.
A simple plan is enough: identify the issue, pause affected flows, communicate with customers if needed, and restore service.
Security checklist for crypto payments
- Restrict access to payment and wallet settings.
- Verify webhook signatures and log events.
- Keep pricing in fiat and display clear payment instructions.
- Use confirmation thresholds for high‑value orders.
- Secure wallets with multi‑signature approvals.
- Document an incident response plan.
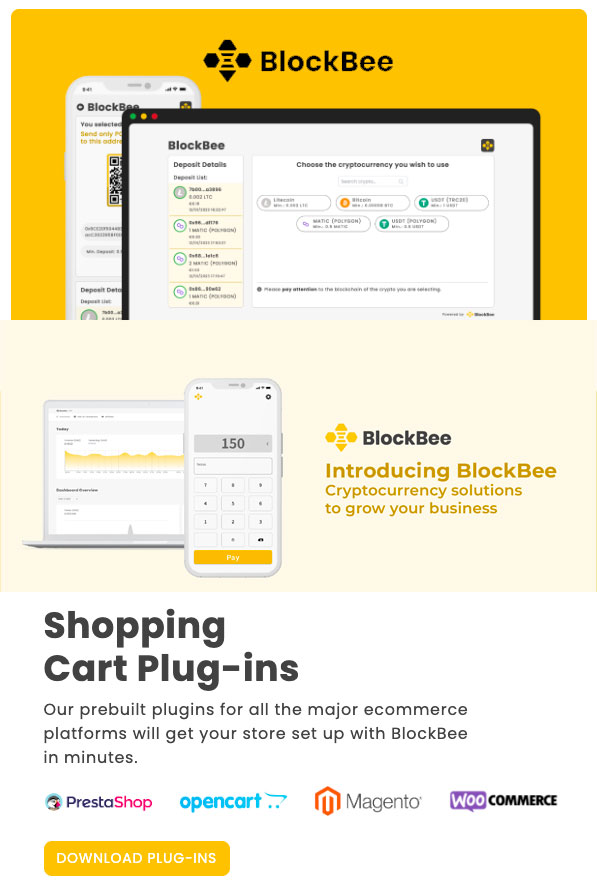
BlockBee and secure payment workflows
BlockBee provides real‑time payment updates and clean transaction records that make security easier to manage. It supports secure checkout flows, reduces manual handling of sensitive data, and keeps order status synchronized. This allows merchants to focus on the business while maintaining strong security standards.
Learn more about secure crypto payments with BlockBee.
Long‑term security maintenance
Security is ongoing. Review access permissions quarterly, rotate API keys when team members change, and audit webhook logs for anomalies. As your crypto volume grows, tighten controls gradually rather than all at once. This keeps the system secure without overwhelming the team.
Strong security does not have to be complex. With consistent practices, crypto payments can be as safe and reliable as any other payment method.
That is the purpose of crypto payment security best practices: protect revenue while keeping checkout simple and fast.
Environment separation and testing
Use separate environments for testing and production. Payment credentials should never be shared across environments. In staging, test the full flow: payment creation, webhook confirmation, order update, and refund handling. This prevents surprises in production and helps your team catch edge cases early.
When changes are required, deploy them to staging first, verify that webhooks still work, and then roll them into production. A disciplined release process is a security practice, not just a development habit.
Data retention and privacy
Only store the data you need. For crypto payments, the transaction hash and fiat value are usually enough. Avoid storing unnecessary wallet details or sensitive customer data. This reduces risk in the event of a breach and keeps your compliance footprint smaller.
Make sure your privacy policy reflects how crypto transactions are handled. Transparency builds trust and reduces support questions.
Protecting against configuration drift
Security issues often come from small configuration changes over time. Document your payment settings and review them periodically. If a new team member changes a webhook URL or settlement setting without documentation, errors can go unnoticed. A simple checklist keeps the system consistent and prevents silent failures.
Configuration discipline also makes it easier to diagnose issues when something goes wrong.
Customer‑facing trust signals
Security is also about perception. Customers should feel confident that the payment is legitimate. Use consistent branding on checkout pages, display SSL indicators, and provide a clear support contact. A short confirmation email with a transaction reference reassures customers that the payment is tracked.
Trust signals reduce abandonment and support tickets, which protects both revenue and reputation.
Related guides: Crypto payment risk management: policies that protect revenue | Crypto payment fraud prevention: reduce risk without blocking good orders | Top Noise-Canceling Headphones Under $200: Best Picks for Budget Buyers
FAQ
What are crypto payment security best practices?
Crypto payment security best practices are controls that protect wallets, API keys, and payment confirmations.
How do multi\\u2011signature wallets fit crypto payment security best practices?
Multi\\u2011signature wallets fit crypto payment security best practices by requiring multiple approvals for transfers.
Why are webhook signatures part of crypto payment security best practices?
Webhook signatures are part of crypto payment security best practices because they prevent spoofed payment updates.
How often should keys rotate in crypto payment security best practices?
Key rotation in crypto payment security best practices should follow a defined schedule and after any incident.
Do access controls matter in crypto payment security best practices?
Yes, access controls matter in crypto payment security best practices by limiting who can change payout settings.
How do confirmations affect crypto payment security best practices?
Confirmations affect crypto payment security best practices by reducing double\\u2011spend risk before fulfilling orders.
What monitoring is recommended in crypto payment security best practices?
Crypto payment security best practices recommend monitoring for unusual payout requests and API activity.
How do backups support crypto payment security best practices?
Backups support crypto payment security best practices by ensuring wallet keys and configs are recoverable.
What role does least privilege play in crypto payment security best practices?
Least privilege is central to crypto payment security best practices because it limits damage from compromised accounts.
What is the first step in crypto payment security best practices?
The first step in crypto payment security best practices is securing admin access and API credentials.
Editorial Q&A
Q: What are baseline controls for crypto payment security best practices?
A: Velocity limits, manual review for high-value orders, and clear refund rules.
Q: How do we detect abuse with crypto payment security best practices?
A: Watch for unusual order spikes, mismatched shipping details, and repeated attempts.
Q: How do we monitor crypto payment security best practices over time?
A: Track refund rates, disputes, and anomalies to refine rules continuously.
Q: How do we avoid blocking good buyers in crypto payment security best practices?
A: Keep rules light and review only the highest-risk transactions.
Q: Should we restrict regions for crypto payment security best practices?
A: Only if your risk policy requires it, and document the reasoning internally.











Join the discussion
Share a real experience or ask a focused question. Short replies are perfect.